TUESDAY: 2 August 2022. Morning paper. Time Allowed: 3 hours.
This paper has two sections. SECTION I has twenty (20) short response questions of forty (40) marks. SECTION II has three practical questions of sixty (60) marks. All questions are compulsory. Marks allocated to each question are shown at the end of the question.
SECTION I
1. __________multiplexing uses available bandwidth of communication channel to be shared among multiple users by frequency by translating or modulating each of the individual users to different carrier frequency. (2 marks)
2. What is the media access control (MAC) method used in Ethernet Technology for Local Area networking to mediate media Contention? (2 marks)
3. Which Multiplexing technique allows each device same time slot to transmit data over the link irrespective of the device status on data transmission? (2 marks)
4. __________is commonly used to convert a signal in the time spectrum to a frequency spectrum. (2 marks)
5. ____________is a modulation pattern for conditioning communication signals for transmission. (2 marks)
6. What is the upper sub layer of the layer 2 of the OSI Model that acts as an interface between the network layer and the medium access control (MAC) sub layer?
7. Which service discovery protocol is used for name-to-IP address resolution? (2 marks)
8. The wide-area network (WAN) technology mode for switching and transmission that efficiently and flexibly organises information into cells is known as_________________ . (2 marks)
9. Which protocol manages the conversation between end devices and guarantees the reliable delivery of information? (2 marks)
10. Identify the fiber optic cable shown below.

11. What is the name given to a set of communication standards to transmit data, voice, and signaling using digital lines as copper? (2 marks)
12. What is the deviation such as amplitude or phase timing of signal pulses in a high frequency digital signal? (2 marks)
13. _____________is used in enterprise deployments to manage groups of lightweight access points. (2 marks)
14. Which switched communication network is associated with the following characteristics? (2 marks)
• It is capable of handling the data that is digital and the traffic because of voice signals.
• The connection of the network allows transferring the ‘electrical current’ along with the voice signal.
• It is a ‘Connection-Oriented’ process.
15. Which wireless standard is best suited for industrial and IoT environments due to its short-range and low data-rates? (2 marks)
16. An upcoming agribusiness enterprise sought tenancy in one of the tallest building in your vicinity. They got one isolated room at the top most floor of the building. After network testing is complete, the Network Administrator reports that the wireless LAN signal is occasionally affected by some type of interference. What is a possible cause of the signal distortion? (2 marks)
17. ____________is a signaling protocol used for initiating, maintaining, and terminating real-time sessions that include voice, video and messaging applications? (2 marks)
18. Which protocol is a standard networking protocol that enables a central wireless LAN Access Controller (AC) to manage a collection of Wireless Termination Points? (2 marks)
19. Modulation is the process by which information is encoded into electrical signals for transmission over a medium. What is the modulation technique used in 802.11ax standard? (2 marks)
20. In networking _________is an expression of how much time it takes for a data packet to travel from one designated point to another. (2 marks)
SECTION II
21. Create a word processor document named Question 21 and use it to save solutions to questions 1 to 4 below. Save your solutions in form of screenshots.
Examine the diagram below and answer the questions that follow:
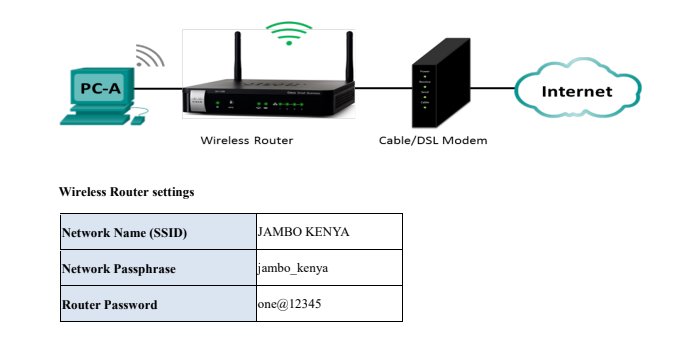
Required:
In question 21 document, explain how you would perform the following tasks:
Display the configuration for SSID (4 marks)
Display the configurations of wireless security password using WPA2 settings (6 marks)
Configure the router to use 192.168.10.0/27 as DHCP network address to end devices (6 marks)
Show configuration of starting and ending IP Addresses. (4 marks)
Upload question 21 document
(Total: 20 marks)
22. Create a word processor document named Question 22 and use it to save solutions to questions 1 to 5 below. Save your solutions in form of screenshots.
1. From your computer, capture a screenshot showing the default gateway IP address of the router. (3 marks)
2. Capture a screenshot showing the physical address of your PC. (3 marks)
3. Capture a screenshot showing connectivity between your computer and www.familyradio316.com.(4 marks)
4. From the PC use appropriate command utility to trace the path to www.google.com. (4 marks)
5. Capture a screenshot displaying the host name of the computer you are using. (6 marks)
Upload question 22 document
(Total: 20 marks)
Network Name (SSID) JAMBO KENYA
Network Passphrase jambo_kenya
Router Password one@12345
23. Create a word processor document named Question 23 and use it to save solutions to questions 1 to 5 below. Save your solutions in form of screenshots.
Using appropriate simulator, setup the topology as shown below:
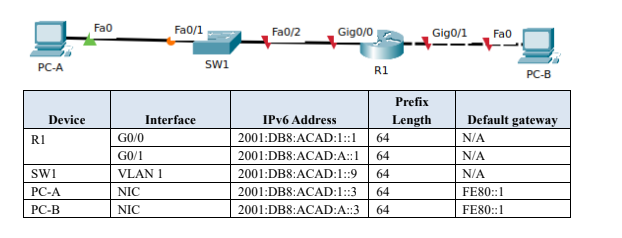
Required:
1. Configure IPv6 to all the devices (6 marks)
Capture a screenshot of the output
2. Using appropriate command, assign the device name to the intermediary devices (4 marks)
Display the device names
3. Using appropriate command, prevent the router and switch from attempting to translate incorrectly entered Command as though they were hostnames.
Capture a screenshot of the commands (4 marks)
4. Assign Kenya@59 as the privileged EXEC encrypted password for both router and switch
Capture a screenshot of the encypted password (4 marks)
5. Test connectivity between PC-A and PC-B (2 marks)
Upload question 23 document
(Total: 20 marks)
