Information Systems
INTRODUCTION
In the previous 4 chapters we have looked at how information systems are supporting various business functions such as sales and marketing, finance and accounting and human resources. We also looked at how information systems are helping businesses achieve greater integration. We explored the growing impact of e-commerce on the different functions.
In this chapter the following topics are discussed:
- Acquiring information systems
- System development
- Security and control
ACQUIRING INFORMATION SYSTEMS
Organisations acquire information systems mainly to enable them to improve the efficiency of the operations, to provide management information to improve decision making organisation. This section examines the two main sources of information systems, which are:
- Purchase ready-made application software packages.
- Development of custom built systems (also referred to as bespoke systems).
Ready-Made Software Packages
The type of application required by a company depends on the nature of the business involved. Some application packages are specific to a particular business sector, while other packages are more general and are used by many different types of business. These two categories of application are called Horizontal and Vertical Applications.
- Horizontal Applications: These are applications such as Sales Order Processing, Inventory and Payroll systems that are applicable across a range of industrial sectors.
- Vertical Applications: These are applications that are specific to a particular business sector such as, Hospital Administration, Banking and Insurance applications.
If the business sector is large then it is likely that there will be a large choice of suitable packages available. However when a particular business sector is limited in size to a relatively small number of companies then the number of ready-made packages available may be small or in some case there may be no suitable package available.
Ready-made or Application packages are generally only feasible where the application required is of a standard variety, the kind of system that is likely to be required by a large number of companies
Advantages of Using Application Packages
Application packages purchased offer a number of advantages over custom-built systems.
These advantages include the following:
- Packages are available for use straight away, while custom-built systems can take months to develop.
- Packages are normally in use for some time and will generally be free of errors unlike custom built systems…
- Packages are normally supplied with good documentation.
- Packages are normally upgraded at regular intervals and these upgrades can be purchased by the users…
- Packages are generally cheaper than developing custom built systems.
- The package supplier will normally provide training and support
Disadvantages of Using Application Packages
Application package will not generally be the optimal solution to an organisation’s requirement. The following are the main disadvantages:
- Software packages may not meet all the company’s- needs.
- The software may be difficult if not impossible to modify and may require extensive business process change during implementation
- Purchased software may be difficult to integrate with existing systems
- The software vendor who created the package may cease supporting the application or go out of business
- Support and software licences may work out expensive for the organisation
Custom Built (Bespoke) Systems
For some companies, standard of –the shelf application packages do not provide a solution to their business needs. The companies will need to acquire custom-built systems that have been designed and built to meet their specific needs. Companies, who require custom built systems which are also referred to a bespoke or tailor made systems, normally have two options:
- Develop the system in-house
- Outsource development
In-House Development
This involves system development within the company itself. The work is normally done by Systems Analysts and Programmers employed within the company’s IT department.
Outsourced Development
This approach involves contracting out the development work to a specialist software development company. The software development company will build the system to agreed client specification. This approach can be expensive as any changed (even small) outside the agreed specification can involve substantial additional charges.
Advantages of Custom Built (Bespoke) Systems
The following are the main advantages of custom-built packages:
- They provide the optimal solution to an organisation’s requirement.
- The custom-built system can be designed to interface with existing systems
- Can provide tailored support for desired business processes.
- Minor changes to the system can be implemented at minimal cost (where internally developed).
Disadvantages of Custom Built (Bespoke) Systems
The following are the main advantages associated with custom-built packages:
- It can take a long time to produce a working system.
- Highly skilled systems analyst and programmers are required to develop custom-built systems.
- Custom-built systems are expensive to develop
- Extensive testing of systems are required
- Custom-built packages often experience teething problems when first implemented
- The subsequent maintenance of custom-built systems can be hindered by lack of documentation of the original design. This can be a serious problem where the original programmer has left the company
Evaluating Alternative Software Packages
Rainer, Turban et al 2007 set out the following six step process for selecting a software vendor and an application package.
Vendor and Software Selection Process
STEP 1: IDENTIFY POTENTIAL VENDORS
A company can identify software application vendors through a number of sources including, technical and trade journals, consultants with experience in the particular area, other companies in the industry and Web searches.
Step 2: Determine the Evaluation Criteria
The company will require a detailed set of evaluation criteria which include the following areas:
- Characteristics of the vendor
- Functional requirements of the system
- Quality of the documentation to be provides
- Vendor support of the package
The criteria should be set out in a request for proposal (RFP) document which is sent to potential vendors. They specify that the vendor should supply a list of current users of the system and require a demonstration of the system.
STEP 3: EVALUATE VENDORS AND PACKAGES
The responses to the RFP will be evaluated using the criteria established earlier. Some criteria will have a higher weighting than others. A short list will be prepared of those vendors who achieved the highest overall score.
STEP 4: CHOOSE THE VENDOR AND PACKAGE
Once the short list is ready the company will begin negotiation with these vendors. The following is a list of software selection criteria that could be used to select the application package:
- Fit for Requirements: Does the software meet the essential requirements?
- Cost and financial terms: How much is the purchase cost? Are there additional licences costs and how much?
- Technical Compatibility: Is the application compatible with the existing operating environment?
- Level of Usage: How many other companies are using the package and for how long?
- Upgrade and costs
- Vendors reputation
- Application flexibility and scalability
- Availability of documentation
- Level and cost of training provided
- System security: How secure is the application? What access controls are included?
- System interface and ease of use:
STEP 5: NEGOTIATE THE CONTRACT
The contract price of the software and the amount of support provided. If the system needs to be modified to company’s requirement then detailed specifications must be included in the contract. Details of the acceptance testing to be carried out would also be included.
STEP 6: ESTABLISH A SERVICE LEVEL AGREEMENT
These specify how work is divided between the company and the vendor. SLAs would typically include details such as performance, availability, backup and recovery, upgrades, the level of support to be provided (9-5 or 24-7) and response times to faults on the system.
THE SYSTEM DEVELOPMENT LIFE CYCLE (SDLC)
The system development life cycle (SDLC) is a structured framework that consists of a set of sequential processes that are used to develop information systems. The following are the stages that would be found in a typical SDLC:
- System Investigation (including feasibility study)
- Systems analysis and design
- Programming
- Testing
- Implementation (including conversion or changeover)
- Operation and Maintenance.
The following sections provide an overview of these stages.
System Investigation
The system investigation stage examines the feasibility of the proposed system solution.
Feasibility Criteria
The feasibility may be considered under the following three headings:
- Technical Feasibility
- Operational Feasibility
- Financial Feasibility
TECHNICAL FEASIBILITY
This focuses on the reliabilities/capabilities of the hardware and software to meet the needs of the proposed system, and whether they can be acquired or developed in the required time. The technical feasibility will involve an outline quantification of the data volumes, frequencies, cycle of activities etc and a provisional assessment of the hardware and software needed to service this workload.
OPERATIONAL FEASIBILITY
The operational feasibility focuses on the organisational implications of the proposed computerised system(s). It involves as examination of the potential impact of the system on organisational structure, group relationships and jobs. The costs associated with possible redundancies, redeployment and retraining need to be assessed. The general acceptability of alternative computer systems from a management and employee perspective is considered.
FINANCIAL FEASIBILITY
This focuses on whether expected cost savings, increased revenue, increased profits, and reductions in required investment, and other types of benefits will exceed the costs of developing and operating a proposed system. A cost-benefit analysis may be used to assess the financial feasibility of the proposed system(s). The findings of the feasibility study are presented to management in the form of a feasibility report.
Systems Analysis and Design
The systems analysis stage involves examining the problem that the organisation is trying to solve with an information system. This stage involves defining the problem in more detail, identifying its causes, specifying solutions, and identifying the information requirements that must be satisfied by a system solution.
The purpose of the systems design phase is to show how the system will fulfil the information requirements specified in the system analysis phase. The system designer draws up specifications that will deliver the functionality identified during the systems analysis phase. Both the analysis and design activities are the job of the systems analysts.
SYSTEMS ANALYSTS
The main tasks of the Systems Analyst are:
- Analysing the business processes to identify the requirements for a computerised system.
- Engagement with business users to establish their information system requirements
- Designing the information (computer based) system.
- Drawing up detailed specifications of the programs that need to be written which are supplied to the programmers.
- Organising the implementation of the new and improved systems and their subsequent maintenance
Programming
Programming translates the design specification into software (program code) that provides instructions for the computer. The program code is written by the programmers.
PROGRAMMERS
The main duties of the programmers include:
- Analysing the program specification supplied by the Systems Analyst
- Designing the structure of each program
- Writing the program(s) in a specific program language (e.g. C, Visual Basic, Java etc.)
- Testing the programs to ensure they work correctly and in accordance with the program specification
Testing
Testing is carried out to ensure the system produces the desired result and to detect any errors in the code. The following three categories of testing are normally carried out on a custom built system:
- Program or Unit Testing – this is done by the programmers
- System Testing – this is normally done by the Systems Analysts
- User Acceptance Testing – this is done by the system users
Program or Unit Testing
Each individual program is tested by the programmer to identify and correct errors in the program code.
System Testing
This is carried out on completed system to establish that the system meets its specified requirements.
User Acceptance Testing
Acceptance testing is normally carried out by the end users of the system to ensure that the system meets their requirements. This is the final stage of testing before the system goes live and it involves putting data through the system to see that it performs correctly. The data used will be similar to real business data. Any defect found will be reported to the developers and when corrected will be retested.
Implementation
The implementation phase is used whether the system is built or purchased as a package. The level of problems experienced during the implementation phase is likely to vary depending on whether the system is a custom built or purchased package.
The implementation phase involves a number of tasks that must be planned, organised and controlled. The main tasks required are:
- Software Installation
- User Training
- System Conversion or Changeover
Software Installation
The software installation will normally be done by the organisation’s IT personnel or in the case of packaged software; it may be done by the external software supplier
User Training
As systems become more complex the need for training becomes more important. If the benefits expected from the installation of a computerised based system are to be achieved it is essential that the users know how to use the system and understand why the system is being introduced.
The typical components of the user-training program involve:
- Selection
The manager of the particular department or area affected by the introduction of the new system will select the people that need to be trained.
- Identify Training Requirements
The training requirements will be identified based on the changes that result from the new system introduction
- Planning Training Sessions
The aim of the training sessions is to give users the specific skills to use the new system effectively. Training sessions should be primarily practical activity involving users performing tasks on the systems. This is because people learn better by doing than by listening and watching.
- Delivering the Training
If the system is developed in-house by the IT Department then they are most likely to deliver the training. The training could also be delivered by one of the users who are first trained themselves. If an external supplier provides the new system, the supplier will usually provide the training for a fee.
- Computer Based Training (CBT)
The use of computer-based training is a lower cost option than instructor led training. It also allows users to learn at their own pace.
System Conversion or Changeover
A critical part of the implementation stage is the system conversion or changeover. System conversion or changeover is the process involved in changing from the old system to the new system. There are four main approaches to conversion: parallel running, direct cutover, pilot conversion and phased conversion.
PARALLEL RUNNING
Parallel running involves operating the old and new systems simultaneously for a period of time, until it is established that the new system working correctly. Both systems process the same data and the outputs are compared. The main advantage of this approach is that if a problem is discovered in the new systems users can revert to the old system until the problem is solved. The main disadvantages with this approach relate to difficulty and cost in both time and money of having to update two systems and danger of data input error. In many situations this is not a viable approach
DIRECT CHANGEOVER
This method involves a complete replacement of the old system with the new system at a particular point in time. The direct changeover method is probably the most straightforward and least expensive method. It is also the most risky approach because there is no fallback if the new system doesn’t work as planned.
PILOT CONVERSION
A pilot conversion involves implementing the system in one part of the organisation such as in one functional area. The system is assessed during the pilot and if working successfully it is implemented in other parts of the organisation.
PHASED CONVERSION
Phased conversion involves introducing parts of the systems in stage which could be one module at a time. Each module is assessed and if working correctly then more modules are introduced.
Operation and Maintenance
Once the new system is implemented it will operate for a period of time until it is upgraded or replaced. During this period the system will be assessed to establish if it is operating correctly and if it needs to be changed.
The term system maintenance is generally used to describe all changes made to a computer system after initial implementation.
There are three main types of maintenance:
- Corrective Maintenance: This is to fix errors or omissions may have been discovered in the system after it has gone into production
- Adaptive Maintenance: The business environment is dynamic and subject to constant change and these changes need to be incorporated into the systems if they are to remain useful
- Enhancement Maintenance: Experience of using the system will often show that improvements and enhancements to the system are needed.
Over its lifetime a system will normally go through many maintenance phases.
D. SECURITY AND CONTROL
This section describes the major risks to computer security and the main control measures that can be taken to protect against those threats. Disaster recovery planning is also briefly discussed
Risks and Threats to Information Systems
The data stored in organisation’s files and databases is a critical asset to the business, and must be protected from a range of risks and threats.
Causes of Vulnerability
A number of factors related to the nature of an organisation’s computerised environment make it especially vulnerable to risks and threats. Laudon and Laudon highlight the following contributing factors:
- Data are stored in electronic format and are therefore are not visible or easily auditable.
- Data are concentrated in electronic files and databases. A disaster such as a hardware or software fault, power failure or fire could destroy organisation’s entire records
- There may not be a visible trail to indicate what occurred for every computer process so errors entered in data can be very difficult to detect.
- Computer programs are also vulnerable as errors can be accidentally introduced when updates to the programs are installed.
- Many information systems can be accessed through telecommunications, and telecommunications can produce errors in data transmission.
- Data in files or databases can be accessed and manipulated directly in online systems.
The data can be stolen, corrupted or damaged by hackers and computer viruses.
- Hardware equipment such as mobile computing devices can be stolen
Types of Risk and Threats
The main threats to an organisation’s information systems include the following:
- Malicious software
- Hackers
- Threats from employee
- Software errors
Malicious Software
Malicious software, also referred to as malware, is any program or file that is harmful to a computer user. Malware includes computer viruses, computer worms, Trojan horses, spyware and keyloggers.
Virus: A computers virus is a small program or programming code that replicates itself by being copied or initiating its copying from one file to another.
Worms: A computer worm is a self-replicating virus that resides in active memory and duplicates itself but does not alter files.
Trojan horse: A Trojan horse is a program in which malicious or harmful code is contained inside what appears to be harmless programming or data in such a way that it can get control and execute some form of damage to the computer system. A Trojan can also give a hacker remote access to a targeted computer system.
Like a virus and worms, a Trojans can also harm a computer system’s data or performance.
Spyware: These are programmes that are resident in computers and gather information about a computer user without their knowledge.
Keyloggers: These record keystrokes made on a computer by the person using the keyboard to discover login names and passwords, bank account numbers etc…
Hackers
A hacker is an individual who intends to gain unauthorised access to a computer system. Hackers gain access to the systems by finding weaknesses in the security protections employed by Web sites or information systems. Hackers can steal information, deface, disrupt or damage a Website or information system.
DENIAL OF SERVICE (DOS) ATTACK
This is where hackers flood a network or Web server with thousands of false requests for service in order to crash the network of server
SPOOFING AND SNIFFING
Spoofing involves hiding of a hacker’s identity or email addresses, or redirecting a Web link to a different web site setup up by the hacker. The aim of spoofing is to trick users to provide information such as login names and passwords and account information to the outsider.
A sniffer is an eavesdropping program that monitors network information and can enable hackers to steal information transmitting over the network.
Threats from Employee
Some of the largest threats to businesses come from employees. These can include disruptions to service, errors in data entry, accidental deletion if data and diversion of customer credit data and personal information.
Many employees forget their passwords to access computer systems or allow other members of staff to use them, which can compromise the system. Employees can introduce errors by entering faulty data or by not following instructions for processing data and using computer equipment.
Software Errors
Software errors pose a constant threat to information systems as they can cause the system to crash, or slow down operation and can lead to large losses in productivity and in some cases cause losses of data. Software can contain hidden bugs in the program code which in addition to impacting performance can open system to hackers.
To protect against these various threats an organisation will typically implement a range of control measures implement. These are discussed in the next section.
Controls
The purpose of controls is to prevent accident damage, deter deliberate act and intrusion, detect problems and enhance recovery. There are two broad categories of controls:
- General Controls
- Application Controls
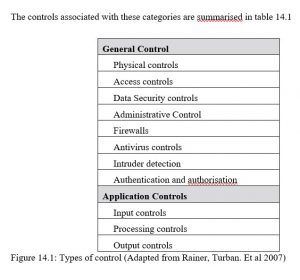
General Controls
General controls protect the overall system environment within an organisation regardless of application. The major categories of general controls include: physical controls, access controls, data security controls, administrative control, firewalls, antivirus controls, intruder detection and authentication and authorisation
PHYSICAL CONTROLS
Physical controls are used to prevent unauthorised physical access to a company’s computer facilities. A typical physical control would the use of swipe cards to gain access to locked computer rooms.
ACCESS CONTROLS
These are used to prevent unauthorised users from accessing an information system. A username and password would be an example of an access control.
DATA SECURITY CONTROLS
Data security controls prevent unauthorised changes, deletion or access to data while the data is in use or in storage. Data security software can be configured to restrict access to individual files, data fields or groups of records
ADMINISTRATIVE CONTROL
These are formalised standards, rules, procedures and control disciplines to ensure the organisations general and application controls are properly executed and enforced.
FIREWALLS
A firewall consists of hardware and software and its purpose is to prevent unauthorised traffic from entering a private or company network from an external network such as the internet. The firewall normally sits between the company’s internal network and an external network and monitors outgoing and incoming messages. It blocks any message that doesn’t conform to specific security criteria that have been programmed into the firewall.
ANTIVIRUS CONTROLS
Viruses are software programmes that infect a computer system, causing loss or damage to software and data. Viruses can enter a computer network in a number of ways:
- On portable memory devices
- From the Internet
- In email attachments
Antivirus programs protect against viruses by either preventing their installation or detecting and removing viruses already installed on a computer system
INTRUDER DETECTION
Intrusion detection systems detect unauthorised intruders trying to access a network. The detection system can be configured to close part of the network if an intrusion is detected.
AUTHENTICATION AND AUTHORISATION
To gain access a user must be authorised and authenticated. Authentication refers to the ability to know that a person is who they claim to be. Authentication is often established by using passwords to log on to a computer system and also by using passwords to access particular systems and files that they have been authorised to access.
APPLICATION CONTROLS
Application controls are designed to protect a specific application. Application controls include input, processing and output controls.
INPUT CONTROLS
Input controls are procedures to check data for accuracy and completeness when they enter the system.
PROCESSING CONTROLS
Processing controls are the routines for establishing that data are complete and accurate during updating. Common controls include control totals, computer matching and run control totals.
OUTPUT CONTROLS
Output controls are measures to ensure that the outputs after processing are accurate, complete and distributed to the correct recipients.
Disaster Recovery Planning
Disaster recovery planning involves specifying plans for the restoration of computing and communications services after they have been disrupted by a natural event such as an earthquake, flood, or some human activity. Disaster recovery plans focuses on getting the systems up and running. It means having data backups available and the maintenance of backup computer systems and having backup telecommunications links in place.
With the increasing importance of information technology for the continuation of business critical functions, it is importance to protect an organisations data and IT infrastructure in the event of a disruption.
TRENDS IN INFORMATION SYSTEMS
This section looks at some recent development in information systems and the internet.
Mobile Computing
Increasingly we are using wireless devices such as smartphones, wireless handheld devices, and laptops with wireless network connections to communicate and to obtain information and data.
Mobile phones are no longer just for voice communications; they are now an important platform for delivering digital data, such as downloading video and music, internet access and e-mail. There are increasingly being used by remote staff such as field sales and service staff to access applications and email. Businesses are using wireless networks and applications to increases productivity and worker output by providing communication and access to information from almost anywhere.
Mobile technology provides more flexible arrangements for organising work as field staff can access details of jobs on their mobile device without having to return to the office for instructions.
Cloud Computing
Cloud computing is a model of computing that provides access to a pool of shared computing resources over a network (usually the internet). These resources include computers, storage, applications and services. These resources are made available to the users based on their needs and independent of the location of the users themselves.
According to Laudon and Laudon (2012) there are basically three types of cloud computing services:
- Software as a Service (SaaS): Customers can use software applications hosted on a service provider’s infrastructure. A wide range of applications can be delivered through a SaaS model, such as customer relationship management, and email. Users are charged a subscription fee on the level of services offered and the numbers of user logins required. An example of a company offering SaaS is Salesforce.com which leases CRM software over the internet.
- Cloud infrastructure as a service: Customers use computer processing, storage, networking and resources from the cloud service provider. For example Amazon sell infrastructure services including storage service for storing customer’s data. Users only pay for the storage capacity used.
- Cloud platform services: Customers use software tools and infrastructure hosted by the service provider to develop their own applications that are then hosted on the servers belonging to the service provider.
The benefits of cloud computing to the business are:
- Large investment in IT infrastructure is not required
- Services are available on-demand
- Charges are based on amount of resources used
- Ability to scale up or down resources as required
Semantic Web
The Semantic Web is an initiative led by the World Wide Web Consortium (W3C) that promotes common formats for data on the World Wide Web. The Semantic Web aims to move for the current situation where the Web is composed of basically unstructured documents into a “web of data”. According to the W3C the Semantic Web is about two things:
- It is about common formats for integration and combination of data drawn from diverse sources, where on the original Web mainly concentrated on the interchange of documents.
- It is also about language for recording how the data relates to real world objects.
The Semantic Web was initially conceived by Tim Berners-Lee, the inventor of the World Wide Web who defines the Semantic Web as “a web of data that can be processed directly and indirectly by machines.”
Virtual Identities
A virtual identity is created when someone logs on to a digital platform or system such as virtual communities, social media and gaming sites. Platforms such as Second Life offer a virtual community where people act through their virtual identity.
Businesses need to understand the impactions of a large section of population (40% who contribute content online do so using user names and pseudonyms) including customers and worker that are using virtual identities to interact with each other, and with businesses.
