THURSDAY: 4 August 2022. Afternoon paper. Time Allowed: 2 hours.
Answer ALL questions. Each question is allocated two (2) marks.
1. The following are regulatory issues that a blockchain application user should consider when using a particular blockchain/distributed ledger protocol EXCEPT?
A. Aware of the inherent risks involved in using a regulated platform to transact.
B. Well advised to use blockchain applications with robust governance frameworks that attempt to resolve the pervasive question of assigning liability.
C. Provide a clearer path to obtaining remedial measures in the event of loss.
D. Contributing as a validator in a blockchain (whether public or private) comes with the responsibility of processing transactions that do not belong to you. (2 marks)
2. Central Bank of Kenya (CBK) as one of the blockchain administrative bodies is responsible for enforcing the following applicable laws and regulations. EXCEPT?
A. Licensing of entities, including revoking licences.
B. Ongoing reporting and monitoring powers.
C. Drafting of industry-specific regulations and guidelines
D. Levying of civil penalties for compliance. (2 marks)
3. Point out the INCORRECT statement.
A. Blockchains work fine for a Large number of users
B. Most of the blockchain technology follow bitcoins infrastructure and use Proof of Work as a consensus algorithm.
C. The public ledger system fuels the system, so full privacy is not the first concern.
D. Many organizations are making blockchain technology a means of transaction. (2 marks)
4. The following are blockchain legal risks apart from one. Which one?
A. Data Privacy
B. Jurisdiction and Dispute resolution
C. Regulatory Risks
D. Vendor risks and untested code (2 marks)
5. Below are some of the MAJOR areas to be considered while developing a blockchain related application apart from one. Which one?
A. Integration and interoperability
B. Regulations and compliance
C. Operating system recovery
D. Privacy and chain management (2 marks)
6. Point out the INCORRECT statement about private/permissioned blockchain
A. Has a built in Access Control layer in the blockchain nodes to Authenticate and Authorize members of the network.
B. The blockchain stores data and the underlying supporting documents.
C. Members have an ability to restrict who can participate in the consensus mechanism of blockchains network.
D. Members have an ability to restrict who can create smart contracts on the blockchain network. (2 marks)
7. The following are the technologies used to implement your own blockchain EXCEPT?
A. Advanced cryptography
B. Custom network protocols
C. Performance optimization
D. Energy Consumption (2 marks)
8. Point out the INCORRECT statement about blockchain risks.
A. The accuracy of the data underlying the digital record is guaranteed.
B. Concerns over the privacy and accessibility of data on public blockchains.
C. Upgrades could be challenging for obsolete early blockchain versions.
D. Blockchains are not yet as scalable as existing commercial transaction systems. (2 marks)
9. Below are some of the issues that Blockchain must address to become the straightforward and cost-effective alternative to conventional remittance. Apart from one. Which one?
A. Blockchain remittance uses cryptocurrency, the ambiguity of regulations will be a significant issue. It becomes a bigger threat since financial institutions are part of conventional remittance.
B. Blockchain remittance platforms use cryptocurrencies or bridge tokens. So, customers do not have to use their bank accounts to get the cryptocurrency which is convenient.
C. The reliance on cryptocurrency means the impact of its volatility. Even though experts suggest stable coins as the solution, these coins may not be as popular as volatile cryptocurrencies.
D. Even though ATMs in remote locations are a solution, blockchain remittance needs an active internet connection for almost everything. This reliance could be a problem. (2 marks)
10. Which one of the following does NOT make blockchain ideal for fighting financial crimes in Kenya.
A. The technology allows independent verification reliance on third parties.
B. Transactions are recorded in immutable chronological order.
C. Records stored in the blocks are contained in millions of computers participating in the chain; making fraud logistically much more difficult.
D. The blockchain is insecure and non-transparent. (2 marks)
11. Incorporating ‘privacy by design,’ you are helping to minimize the risk of data loss. If you design your projects, processes, and systems with privacy in mind, you can identify problems early on and raise the level of awareness for privacy concerns in the organization. Below are some of the situations in which we incorporate privacy by design in our IT systems APART from?
A. Deploying any new IT infrastructure that stores or processes personal data
B. Implementing new security policies or strategies
C. Sharing data with internal staff
D. Using data for any analytical purposes (2 marks)
12. Which of the following BEST describes Boot Strapping.
A. Moving the existing contracts or business documents/frameworks to the new Block Chain based methodology presents a significant set of migration tasks that need to be executed.
B. Introducing new laws to monitor and regulate the industry for compliance.
C. The basis of Block Chain technology relies on the very fact that it is mathematically impossible for a single party to game the system due to lack of needed compute power.
D. Bitcoin currency reaching yearly highs in both volume and price. (2 marks)
13. Which of the following is incorrect about unpermissioned ledgers.
A. They have a single owner
B. Allow anyone to contribute data to the ledger and for everyone in possession of the ledger to have identical copies.
C. Participants maintain the integrity of the ledger by reaching a consensus about its state
D. They can be used as a global record that cannot be edited
14. Which of the following is NOT an important property of block chain technologies.
A. Reconciliation Through Cryptography
B. Replicated digitally-informed leadership
C. Granular Access Control
D. Granular Transparency and Privacy (2 marks)
15. Which of the following is false about regulating distributed ledgers via legal codes.
A. Regulating a permissioned distributed ledger system is simply a matter of imposing legal obligations on its proprietor.
B. Regulating an unpermissioned system like Bitcoin via legal code is more complicated, as there is no single legal entity in control of the system.
C. Comprises software and protocols, that emerge from the public sector
D. A well-known example of regulating Bitcoin via legal code is the BitLicense (2 marks)
16. In contrast to conventional private financial networks like Visa, ____________ distributed ledger systems lack a central legal entity with formal responsibility over the system.
A. Permissioned
B. Private
C. Unpermissioned
D. Public (2 marks)
17. A _____________ is the common term used for a business license for virtual currency activities, issued by the New York State Department of Financial Services (NYSDFS) under regulations designed for companies.
A. Blockchain
B. BitLicense
C. Crypt money
D. CryptLicense (2 marks)
18. Regulatory regimes have many advantages and disadvantages in the crypto assets industry, as in every industry.
Which of the following is NOT a challenge of regulating crypto currency?
A. Classification
B. Over regulation
C. Value
D. Blockchain revolution (2 marks)
19. How is virtual currency treated for federal tax purposes?
A. Fund
B. Property
C. Product
D. Revenue (2 marks)
20. Which of the following is TRUE about determination of value of virtual currency in fair market?
A. Taxpayers will be required to determine the fair market value of virtual currency in U.S. dollars as of the date of payment or receipt.
B. Taxpayers will be required to determine the fair market value of virtual currency in Kenya Shillings as of the date of payment or receipt.
C. Virtual currency is not treated as currency that could generate foreign currency
D. Depends on whether the virtual currency is a capital asset in the hands of the taxpayer (2 marks)
21. _______________is the unauthorized and intentional use of a name, business name, trademark, domain name or other word or phrase that is registered, owned or in use by another person.
A. Phishing
B. Identity theft
C. Cybersquatting
D. Cyberterrorism (2 marks)
22. _____________ is the dishonest or fraudulent use of an electronic signature, password or the unique identification feature of another person.
A. Identity theft
B. Phishing
C. Cybersquatting
D. Eavesdropping (2 marks)
23. The list below is of Blockchain protocols. Which ONE is NOT?
A. Public Blockchain
B. Consortium Blockchain
C. Private Blockchain
D. Legacy Blockchain (2 marks)
24. What is on-chain governance as used in Blockchain technology?
A. A system for joining together to cryptocurrency Blockchains in a network.
B. A system for protecting Blockchains from illegal transactions.
C. A system for managing and implementing changes to cryptocurrency Blockchains.
D. A system for exchanging cryptocurrency transactions in Blockchains.
25. The following is a list of KEY issues that present risks to firms using Blockchain. Select the ODD one out.
A. Similar jurisdictions
B. Cyber-attacks
C. Data protection
D. Privacy compliance (2 marks)
26. What is the term given to a group of people who come together without a central leader or company dictating any of the decisions?
A. Blockchain autonomous forum
B. Decentralized autonomous organization
C. Unique autonomous forum
D. Beyond boundary independent group (2 marks)
27. The list below consists of Blockchain technology uses in providing intellectual property protection. Which ONE is NOT?
A. Ownership rights
B. Reducing counterfeit
C. Registering trademarks
D. Central Depository Licensing (2 marks)
28. Which of the following is an exit scam in cryptocurrency?
A. Promoters of a cryptocurrency disappearing with investors’ money during or after an initial coin offering.
B. The owners of cryptocurrency threaten to pull out their initial investment.
C. A false scare cryptocurrency collapse created by media houses after an initial coin offering.
D. A threat by influential countries to ban cryptocurrency in during initial coin offering. (2 marks)
29. The following are some regulatory challenges with respect to crypto assets. Which ONE is NOT?
A. Complexity of the technology
B. Rapid changing nature of the technology
C. The global nature of technology
D. Centralized nature of technology (2 marks)
30. What is the BEST use case for smart contracts in Blockchain technology?
A. Digitalize and automate legally binding contracts using artificial intelligence (AI).
B. Enforce the execution of contracts in the legal system using cryptocurrencies.
C. Ensure automatic payments by predetermined actions or events in insurance contracts.
D. Extend the Bitcoin blockchain, the best-known smart contract platform, to the judicial system. (2 marks)
31. How can Blockchain technology be used to help securing identity data?
A. By eliminating third parties through providing secured-data storage at a user’s server.
B. By encoding all the health data and save it on a private and permission less Blockchain.
C. By protecting data that has been submitted on the internet using a cryptographic algorithm.
D. By providing information personal data without disclosing the actual data that proves it. (2 marks)
32. Which of the following is a typical example of how a government actively promotes the use of Blockchain technology?
A. A government introduces a regulatory sandbox that allows a country to closely monitor the experiments in Blockchain mining and design their own cryptocurrency.
B. A government offering e-Residency software, which is available to anyone in the world interested in operating a business online.
C. A government establishes central bank digital money for payments between banks using distributed ledger technology.
D. A government allows citizens to freely do what they want regarding Blockchain and cryptocurrency. (2 marks)
33. The factors below determine the value of a cryptocurrency. Which ONE is does NOT?
A. Node Count
B. Stock Market Listing
C. Rising demand
D. Mass Adoption (2 marks)
34. From the list below select a probable reason why Bitcoin consumes so much electricity.
A. Bitcoin’s centralized structure requires a lot of energy.
B. Bitcoin servers are huge in size and use a lot of electricity.
C. Proof of work consensus mechanism requires a lot of power.
D. Bitcoin uses smartphones that require a lot of energy. (2 marks)
35. Blockchain ______________ is the ability of different Blockchain networks to exchange and leverage data between one another and to move unique types of digital assets between the networks’ respective Blockchains.
A. Transaction
B. Mining
C. Fork
D. Interoperability (2 marks)
36. What might Central bank of Kenya need before backing digital currency?
A. Reassurance that the blockchain does not have in-built weaknesses
B. Enhanced regulatory rules for crypto-currencies
C. Assurance that blockchain ledger systems are secure, fast and reliable
D. A way to link its own payments processing system to blockchain (2 marks)
37. Cryptocurrency poses a risk to both banks and lawyers. Select the possible reason for this.
A. Because it reduces the size of their market.
B. Because they do not typically recruit people who are experts in this type of area.
C. Because they have typically acted as intermediaries in transactions and the blockchain ledger essentially puts them out of a job.
D. Because soon many aspects of what they do will be public in the blockchain ledger. (2 marks)
38. What is ONE of the main difficulties with an unregulated currency?
A. They typically experience surges in value that have no strong link to underlying economics.
B. Consumers are more likely to be ripped off by fake currency exchanges.
C. Regulators cannot enforce fines on crypto-currency exchanges.
D. Consumers do not yet have the right to claim compensation. (2 marks)
39. Why do people think Bitcoin and Blockchain are more trustworthy than traditional currencies and contracts?
A. Because there is no central bank to manipulate the exchange rate.
B. Because the system is built to continually verify and authenticate data.
C. Because it functions by distributing trust – it is open-source and peer-to-peer.
D. Because there is a high level of encryption within the blockchain. (2 marks)
40. Blockchain is NOT easy to regulate. Suggest a reason for this
A. Because its development so far has thrived on the basis of anonymity
B. Because it has already been linked to illegal activity such as the dark web
C. Because the developers remain unknown.
D. Because it is growing so quickly that the regulators are unlikely to catch up (2 marks)
41. Cryptocurrency is crucial to local and international businesses. Select ONE advantage to international businesses.
They can include many other legal documents in blockchains, such as contracts
A. Payments and transaction details are encrypted and therefore far safer
B. It could greatly increase the speed of international payments
C. It could do away with the need to time transactions based on fluctuating exchange rates (2 marks)
42. Bitcoin is considered to be too risky. What is the MOST probable reason for this?
A. Bitcoin may be enormously overvalued – we just do not know yet
B. Bitcoin is largely unregulated
C. The person or people that created Bitcoin remain anonymous
D. Bitcoin was invented only recently and only traditional fiat currencies will retain trust. (2 marks)
43. Select ONE feature that makes Blockchain particularly robust and secure.
A. Blockchain is highly encrypted
B. Blockchain was invented by computer experts rather than financial experts
C. One can access traditional fiat currency since part of it is not online
D. All parties involved in the transaction must agree to alter records (2 marks)
44. What is hoarding as used in cryptocurrency?
A. Buying and holding large amount of crypto artificially raising its price
B. Buying and selling large amount of crypto lowering its price
C. Banks holding large amount of crypto leading to artificial shortage
D. Buyers scrambling for scarce crypto leading to price surge (2 marks)
45. Blockchain is a popular remittance channel. Select ONE likely problem with the current remittance channels.
A. They are not widely accepted
B. They are Expensive
C. They are not online
D. They lack acceptance (2 marks)
46. ___________is a process where some form of assets is converted to digital form that can be moved, stored, or recorded on a Blockchain.
A. Mining
B. Forking
C. Tokenization
D. Scalability (2 marks)
47. The following are types of arbitration that can be done in Blockchain technology. Which ONE is NOT?
A. Judicial arbitration
B. Contractual arbitration
C. Stipulation arbitration
D. Executable arbitration (2 marks)
48. Below is a list of Blockchain development risks. Which ONE is NOT?
A. Underdeveloped standards
B. Decentralized autonomous
C. High energy demand
D. Data privacy legislation (2 marks)
49. Technology ______ is the freedom of individuals to choose the most appropriate technology adequate to their needs and requirements.
A. Neutrality
B. Needs
C. Independence
D. Power (2 marks)
50. The figure below shows a type of transaction where a person’s identity is unknown, but it is possible to assign actions to the same person. What is name given to such a relationship in Blockchain.
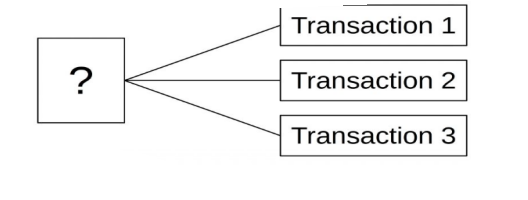
A. Anonymity
B. Pseudonymity
C. Unity
D. Immutability (2 marks)
