KCSE Past Papers Computer Studies 2013
3.23.1 Computer Studies Paper 1 (451/1)
SECTION A (40 marks)
Answer all the questions in this section in the spaces provided.
1 State one function for each of the following elements of a computer system:
(a) hardware; (1 mark)
(b) software; (l mark)
(c) liveware. (l mark)
2 Explain two health issues that could arise from the use of an unsuitable computer desk. (4 marks)
3 List the two categories of system software. (1 mark)
4 Explain two contents of a warranty that should be considered when purchasing computer hardware. (4 marks)
5 Students of a school intend to elect their school captain by secret ballot. State three ways in which computers can be used to improve the election process. (3 marks)
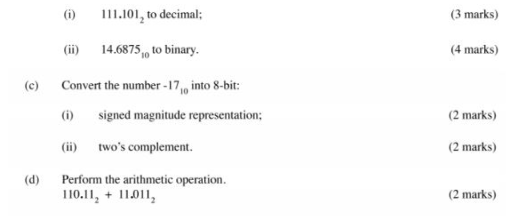
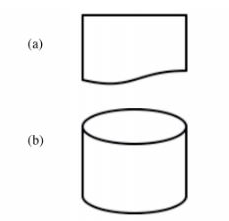
6 Figure 1 and figure 2 show icons representing commands used to manipulate graphics in a desktop publishing package.

Explain the use of each of the icons labelled figure 1 and figure 2. (2 marks)
7 Give two differences between a Graphical User Interface (GUI) and a Commandline Interface. (4 marks)
8 Identify each of the following symbols as used in a system flowchart.
9 A student typed a letter in a wordprocessor and the last line of the letter flowed to the second page.
State three ways in which the student could have adjusted the letter to fit on one page without changing the paper size. (3 marks)
10 A computer user is unable to retrieve a file stored in a server in an organisation. State three reasons why the user would need to contact the network administrator. (3 marks)
11 State three ways in which mobile phones have affected money transactions in the country. (3 marks)
12 State two items that an electronic mail should have for it to be sent. (2 marks)
13 List four devices that use scanning technology that would be used to capture data directly from the source. (2 marks)
14 State two ways in which hardware failure is a threat to data security. (2 marks)
15 Given the binary number 1010] 1 I0] l 1101 l , determine the number of: (a) nibbles; (1 mark)
(b) bytes. (1 mark)
SECTION B (60 marks)
Answer question 16 and any other three questions from this section in the spaces provided.
16 (a) State two advantages of using low level programming languages. (2 marks)
(b) Other than flow charts, state three tools that can be used to present an algorithm. (3 marks)
(c)A form one admission interview consists of four tests; Mathematics, English, Kiswahili and Science. In order to qualify for admission, an applicant must attain a minimum average of 65% in the four tests and not less than 70% in Mathematics. All applicants must sit for the interview. Draw a flowchart that would read the scores for each applicant and determine whether an applicant is successful or not. (10 marks)
17 (a)With the aid of a diagram, describe time sharing mode as used in computer data processing. (5 marks)
(b) A company’s management has opted to use computers to process data. State four factors that the management needs to consider when selecting the company data processing mode. (4 marks)
(c) Explain the purpose of each of the following in system documentation:
(i) user manual; (2 marks)
(ii) sample data; (2 marks)
(iii) table descriptions. (2 marks) 18 (a) State the role of each of the following data communication devices:
(i) repeater; (1 mark)
(ii) router. (1 mark)
(b) Figure 3 shows a network based on the bus topology.
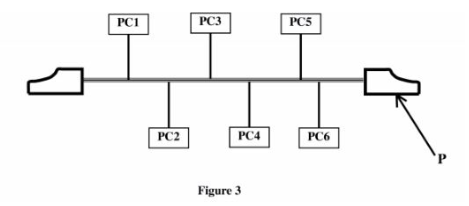
(i) Identify the component labelled P. (1 mark)
(ii) State the function of the component labelled P. (2 marks)
(c) Students of Neema Secondary School formed an environmental club with a goal of taking part in environmental conservation activities. Outline three ways in which they can use the intemet to achieve this goal. (3 marks)
(d) (i) A company has three branches A, B and C where A is the headquarter. The local area network (LAN) at A is directly connected to the LAN at B and directly to the LAN at C. Explain two benefits of having the LAN at B also directly connected to the LAN at C. (4 marks)
(ii) State three Ways in which a company can protect its computer network from hackers. (3 marks)
19 (a) The following is an extract from a document created using a word processor.
CHALLENGES FACING THE YOUTH IN TODAY’S SOCIETY

Identify six formats that have been applied on the extract. (3 marks)
(b) State three tools in a word processor that would help a user to minimize spelling mistakes when creating a document. (3 marks)
(c) The following is an extract of a spreadsheet created to manage sales. Use it to answer the questions that follow.
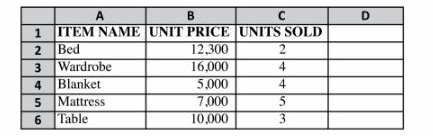
(i) Write a formula that will compute the number of items whose unit price is more than 10,000.
(ii) If the formula = $B2 * C$2 was placed in cell D2, state the output if it was copied to D3. (2 marks)
(d) A school administers examinations to all students in sciences, humanities and languages. Use the entities; EXAMINATIONS, STUDENTS, SCIENCES, HUMANITIES and LANGUAGES to illustrate a network database model.(4 marks)
20 (a) Describe the octal number system.
(b) Convert each of the following to the number system indicated: